OceanBase Cloud Platform (OCP) implements resource isolation at the organization level and provides organization management capabilities. You can manage and grant permissions to roles and users in organizations as needed.
Architecture
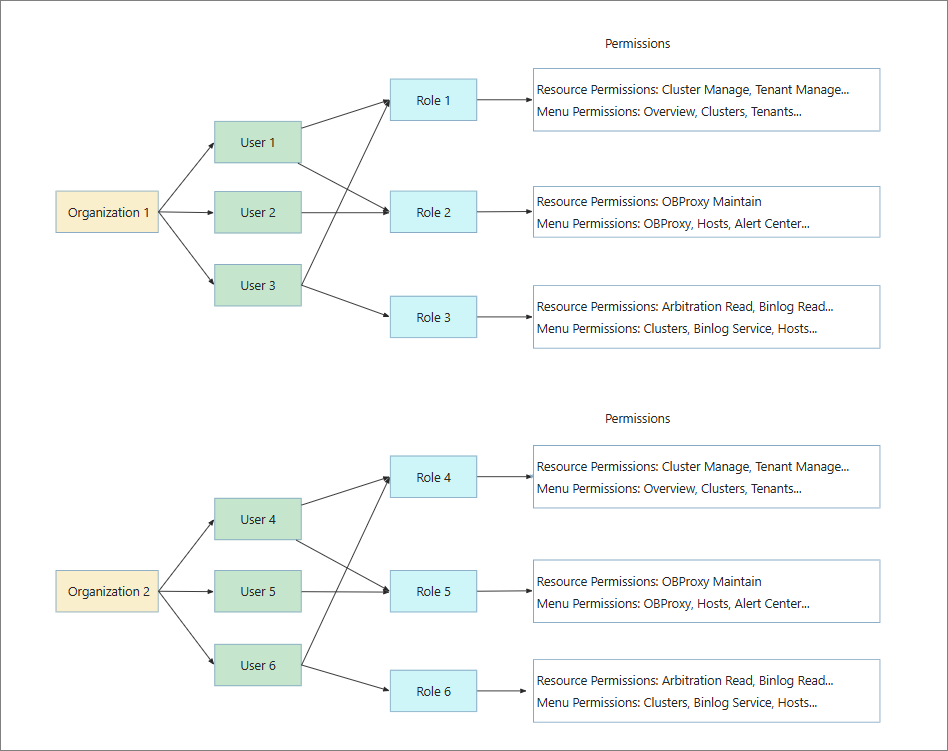
OCP adopts a three-layer management architecture that consists of three types of roles: system administrator, organization administrator, and user. The following figure shows the architecture.
Organization
Organization is a key logical concept and very important in actual application scenarios. For medium- and large-sized enterprises, resources of subsidiaries or departments can be managed and isolated based on organizations. In organization-based resource isolation, each organization is an independent resource space, improving resource management security and precision.
The administrator of an organization has management permissions on the organization and the resources shared with this organization. Specifically, the administrator can manage various types of resources and permissions of roles in the organization.
OCP has two types of organizations: default organizations and custom organizations.
Default organizations
The default organization in OCP is named default. Before you create other organizations, all resources of the system are stored in the default organization.
Custom organizations
You can create custom organizations based on business needs or scenarios and share the resource configurations of an existing organization with a new one. For example, you can share the resource configurations of different clusters with different organizations to implement resource isolation among organizations.
You can search for organizations in the organization list and view information such as the organization name and creation time, and perform common O&M operations. For more information, see Create an organization, View resources of an organization, Share resource configurations, Edit an organization, and Delete an organization.
Role
In OCP, a role is a collection of permissions. A role takes effect only when it is assigned to a user. A user with roles can operate only within the authorized scope. This prevents misoperations from non-professionals and information leakage, thereby ensuring information security.
OCP has two types of roles: default roles and custom roles.
Default roles
Default roles are system-preset roles and can accommodate common permission management requirements. For example, the system administrator role ADMIN that has all management permissions, and the ADMIN_VIEWER role that has all read-only permissions, are default roles.
You can choose System Management > User Management to view all default roles and their permissions on the Role tab.
Custom roles
OCP allows you to create custom roles and assign more fine-grained permissions to custom roles. For example, you can create a custom role that can view only specified clusters or specified tenants in a cluster, and assign the role to a user. You can use custom roles in combination with default ones to provide diversified permission strategies.
On the Role tab, you can search for roles, view information about a role such as the role name, organization, resource permissions, menu permissions, and users to which the role is assigned, and perform common O&M operations. For more information, see Create a role, Copy a role, View a role, Edit a role, and Delete a role.
User
In the OCP console, a user is an operator of system features, and a role is a collection of resource and menu permissions and the carrier of these permissions. A user can perform corresponding operations in the OCP console only when it is assigned one or more roles and have the permissions assigned to the roles. Therefore, the permissions of a user include the permissions of all roles assigned to user. A user must belong to an organization. OCP implements isolation of resources such as OceanBase clusters, tenants, and hosts among organizations to meet enterprise-level permission and role management requirements.
OCP has two types of users: default users and custom users.
Default users
The initial OCP user named admin is a user with the system administrator role and has the permission to manage all clusters and functional modules in OCP.
Custom users
The system administrator can create other users, and assign one or more roles to each user, to enable the users to carry out corresponding responsibilities in the business architecture. For example, the administrator can create a user with the ORG_ADMIN role to enable the user to create other users.
On the User tab, you can search for users, view the information about a user such as the username, role, email address, organization, department, and locking status, and perform common O&M operations. For more information, see View the login history, Create a user, View a user, Edit a user, Copy a user, Change the password of a user, and Delete a user.
Scenarios
When you use the user management feature for the first time, you can perform the following steps for user permission control:
- (Optional) Create organizations and share resource configurations with the organizations. For more information, see Create an organization and Share resource configurations.
- Create roles and grant resource and menu permissions to the roles. For more information, see Create a role.
- Create users and assign roles to the users. For more information, see Create a user.
Limitations
The current OCP version does not support fine-grained permission control on the information collection, plan management, inspection service, alert center, task center, credential management, and system parameters modules.
If you have the read-only permission on any resource, you can view related information of the information collection, plan management, inspection service, alert center, task center, and system parameters modules. If you have the maintenance permission on any resource, you can manage the information collection, plan management, inspection service, alert center, task center, and system parameters modules.
If you have the cluster read-only, tenant read-only, host read-only, or OBProxy read-only permission, you have the read-only permission on all credentials in the credential management module. If you have the cluster maintenance, tenant maintenance, host maintenance, or OBProxy maintenance permission, you have the permission to update all credentials in the credential management module.

