OceanBase Migration Service (OMS) must support the OpenID Connect (OIDC) protocol to adapt to the OAuth 2.0 authentication center. Currently, only the authorization-code mode is supported. This topic describes the configurations to be updated to integrate the OIDC protocol into OMS to implement third-party single sign-on (SSO).
Obtain parameters from the authentication center
You must add your application to the third-party SSO service to obtain parameters required by OIDC, such as the application ID and key.
Parameter |
Description |
|---|---|
| clientId | The client ID of the third-party application. |
| clientSecret | The client secret of the third-party application. |
| scope | The authorization scope. The value is a list of permission IDs separated with commas (,). openid must be included in the value. Example: openid,profile. |
| ClientAuthenticationMethod | The authentication method. Valid values: client_secret_basic (recommended) and basic. |
| jwk_set_uri | The endpoint used to retrieve the public key of the JSON web key (JWK) for decoding the JWK. |
| authorization_uri | The authorization endpoint. |
| token_uri | The endpoint used to obtain a token. |
Configure a callback URL
If the third-party SSO system has a logon callback URL whitelist, you must configure the whitelist.
Set the logon callback URL to http://{serverDomain}/login/oauth2/code/oms, in which serverDomain is the domain name of the server where OMS is deployed.
Deploy OMS
This section describes how to log on to OMS deployed on a single node. If you want to deploy OMS on multiple nodes in a single region or on multiple nodes in multiple regions, see the "Deploy OMS with the configuration file available" section of the Deploy OMS on multiple nodes in a single region or Deploy OMS on multiple nodes in multiple regions topic.
Prerequisites
The installation environment meets the system and network requirements. For more information, see System and network requirements.
A MetaDB cluster is prepared as the OMS MetaDB.
The OMS installation package is obtained. Generally, the package is a
tar.gzfile whose name starts withoms.The downloaded OMS installation package has been loaded into the local image repository of the Docker container.
docker load -i <OMS installation package>The directory to which the OMS container is mounted has been prepared. OMS creates three mapping directories in this directory:
/home/admin/logs,/home/ds/store, and/home/ds/run. These directories store the runtime components and logs of OMS.(Optional) A time-series database is installed to store OMS performance monitoring data and DDL and DML statistics.
Procedure
Log on to the server where OMS is to be deployed.
Optional. Deploy a time-series database.
If you need to collect and display OMS monitoring data, deploy a time-series database. Otherwise, you can skip this step. For more information, see Deploy a time-series database.
Run the following command to obtain the deployment script from the loaded image:
sudo docker run --name oms-config-tool <OMS_IMAGE> bash && sudo docker cp oms-config-tool:/root/docker_remote_deploy.sh . && sudo docker rm -f oms-config-tool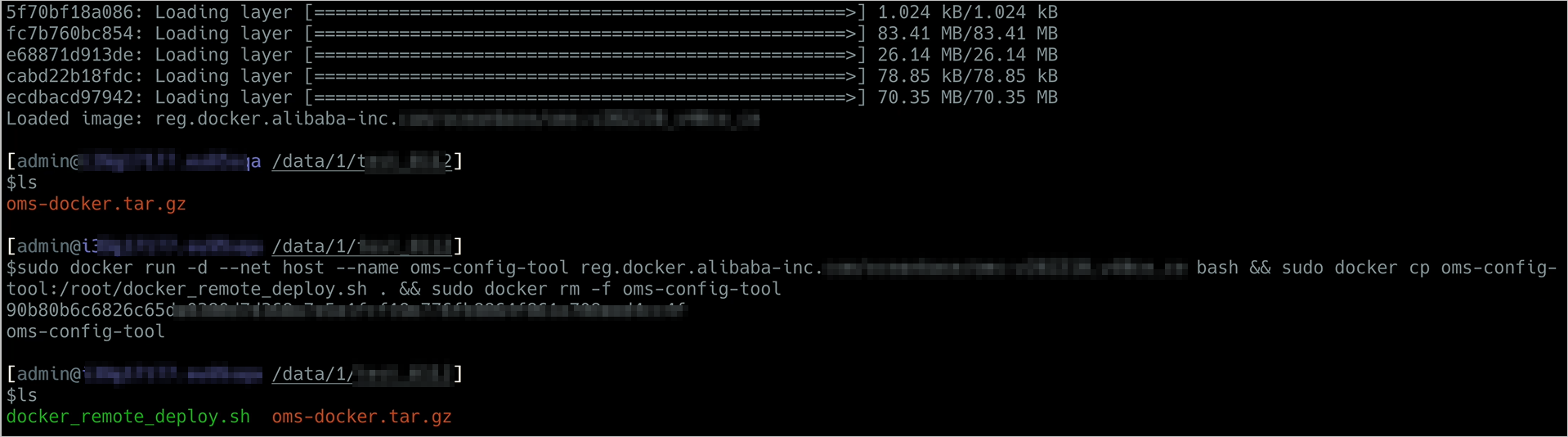
Use the deployment script to start the deployment tool.
sh docker_remote_deploy.sh -o <Mount directory of the OMS container> -c <Directory of the existing config.yaml file> -i <IP address of the host> -d <OMS_IMAGE>Note
For more information about settings of the
config.yamlfile, see the "Template and example of a configuration file" section.Follow the prompts to complete the deployment. After you set each parameter, press Enter to move on to the next parameter.
Select the deployment mode.
Select Single Node in Single Region.
Select the task.
Select Use Configuration File Uploaded with Script Option [-c].
If the system displays "The specified database names already exist in the MetaDB. Are you sure that you want to continue?", it indicates that the database names you specified already exist in the MetaDB. This may be caused by repeated deployment or upgrade of OMS. You can enter
yand press Enter to proceed, or enternand press Enter to re-specify the settings.If the configuration file passes the check, all the settings are displayed. If the settings are correct, enter
yand press Enter to proceed. Otherwise, enternand press Enter to modify the settings.If the configuration file fails the check, modify the configuration information as prompted.
Specify the directory to which the OMS container is mounted in the host.
Use a directory with a large capacity.
Confirm whether the OMS image file can be named as
OMS_IMAGE.If the settings are correct, enter
yand press Enter to proceed. Otherwise, enternand press Enter to modify the settings.Confirm whether to install a Secure Sockets Layer (SSL) certificate for the OMS container.
If yes, enter
y, press Enter, and specify thehttps_keyandhttps_crtdirectories as prompted. If not, enternand press Enter.Start the deployment.
To modify the configuration after deployment, log on to the OMS container and perform the following steps:
Modify the
config.yamlfile based on business needs.Run the
python -m omsflow.scripts.units.oms_init_manager --init-config-filecommand.Run the
supervisorctl restart oms_console oms_drc_supervisorcommand.
Template and example of a configuration file
Configuration file template
Notice
You must replace the sample values of required parameters based on your actual deployment environment. Both the required and optional parameters are described in the following table. You can specify the optional parameters as needed.
In the
config.yamlfile, you must specify the parameters in the key: value format, with a space after the colon (:).
# Information about the OMS MetaDB
oms_meta_host: ${oms_meta_host}
oms_meta_port: ${oms_meta_port}
oms_meta_user: ${oms_meta_user}
oms_meta_password: ${oms_meta_password}
# You can customize the names of the following three databases, which are created in the MetaDB when you deploy OMS.
drc_rm_db: ${drc_rm_db}
drc_cm_db: ${drc_cm_db}
drc_cm_heartbeat_db: ${drc_cm_heartbeat_db}
# Configurations of the OMS cluster
# In single-node deployment mode, the IP address of the server where OMS is deployed is used. We recommend that you use an internal IP address.
cm_url: ${cm_url}
cm_location: ${cm_location}
# The cm_region parameter is not required for single-node deployment.
# cm_region: ${cm_region}
# The cm_region_cn parameter is not required for single-node deployment.
# cm_region_cn: ${cm_region_cn}
cm_is_default: true
cm_nodes:
- ${cm_nodes}
# Configurations of the time-series database
# Default value: false. To enable metric reporting, set the parameter to `true`.
# tsdb_enabled: false
# If the `tsdb_enabled` parameter is set to `true`, delete comments for the following parameters and specify the values based on your actual configurations.
# tsdb_service: 'INFLUXDB'
# tsdb_url: '${tsdb_url}'
# tsdb_username: ${tsdb_user}
# tsdb_password: ${tsdb_password}
# The following table describes the parameters that need to be added when you log on to OMS by using SSO.
oms_iam_auth: OAUTH2
oms_oauth2_user_account_name_field: nickname
oms_oauth2_sso_login_url: http://oms.example/org:8090/omsp/oauth2/authorization/oms?oms_back_url=http://oms.example.org:8090
spring_security_oauth2_client_registration_oms_client_id: xxx
spring_security_oauth2_client_registration_oms_client_secret: xxx
spring_security_oauth2_client_registration_oms_redirect_uri: http://oms.example.org:8090/omsp/login/oauth2/code/{registrationId}
spring_security_oauth2_client_registration_oms_authorization_grant_type: authorization_code
spring_security_oauth2_client_registration_oms_scope: openid,profile
spring_security_oauth2_client_registration_oms_clientAuthenticationMethod: client_secret_basic
spring_security_oauth2_client_registration_oms_provider: oms
spring_security_oauth2_client_provider_jwk_set_uri: https:xxx.com
spring_security_oauth2_client_provider_authorization_uri: https://xxxx/api/auth
spring_security_oauth2_client_provider_token_uri: https://xxx/api/token
Parameter |
Description |
Required |
|---|---|---|
| oms_meta_host | The IP address of the MetaDB, which can be the IP address of a MySQL database or a MySQL tenant of OceanBase Database. Notice: This parameter is valid only in OceanBase Database V2.0 and later. |
Yes |
| oms_meta_port | The port number of the MetaDB. | Yes |
| oms_meta_user | The username of the MetaDB. | Yes |
| oms_meta_password | The user password of the MetaDB. | Yes |
| drc_rm_db | The name of the database for the OMS console. | Yes |
| drc_cm_db | The name of the MetaDB for the CM service. | Yes |
| drc_cm_heartbeat_db | The name of the heartbeat database for the CM service. | Yes |
| cm_url | The URL of the OMS CM service. Example: http://xxx.xxx.xxx.xxx:8088. Note: In single-node deployment mode, the IP address of the server where OMS is deployed is used. We do not recommend that you set it to http://127.0.0.1:8088. The access URL of the OMS console is in the format of IP address of the host on which OMS is deployed:8089. Example: http(https)://xxx.xxx.xxx.xxx:8089. Port 8088 is used for program calls, and Port 8089 is used for web page access. You must specify Port 8088. |
Yes |
| cm_location | The code of the region. Value range: [0,127]. You can select one number for each region. | Yes |
| cm_region | The name of the region. Example: cn-jiangsu. Notice: If you use OMS with the Alibaba Cloud Multi-Site High Availability (MSHA) service in an active-active disaster recovery scenario, use the region configured for the Alibaba Cloud service.`` |
No |
| cm_region_cn | The value here is the same as the value of cm_region. | No |
| cm_nodes | The IP addresses of servers on which the OMS CM service is deployed. | Yes |
| cm_is_default | Indicates whether the OMS CM service is enabled by default. | No. Default value: true. |
| tsdb_enabled | Indicates whether metric reporting is enabled for monitoring. Valid values: true and false. |
No. Default value: false. |
| tsdb_service | The type of the time-series database. Valid values: INFLUXDB and CERESDB. |
No. Default value: CERESDB. |
| tsdb_url | The IP address of the server where InfluxDB is deployed. You need to modify this parameter based on the actual environment if you set the tsdb_enabled parameter to true. |
No |
| tsdb_username | The username used to connect to the time-series database. You need to modify this parameter based on the actual environment if you set the tsdb_enabled parameter to true. After you deploy the time-series database, manually create a user and specify the username and password. |
No |
| tsdb_password | The password used to connect to the time-series database. You need to modify this parameter based on the actual environment if you set the tsdb_enabled parameter to true. |
No |
| oms_iam_auth | The logon method. Valid values: OAUTH2 and LOCAL. OAUTH2 is compatible with the password-based logon method. |
Yes |
| oms_oauth2_user_account_name_field | The field used to obtain the username from IdToken. Example: nick or nickname. | Yes |
| oms_oauth2_sso_login_url | The logon URL in the http://{serverDomain}/omsp/oauth2/authorization/oms?oms_back_url={serverDomain} format. {serverDomain} is the domain name and oms_back_url is the OMS page displayed after the logon succeeds. |
Yes |
| spring_security_oauth2_client_registration_oms_client_id | The client ID of the third-party application. | Yes |
| spring_security_oauth2_client_registration_oms_client_secret | The client secret of the third-party application. | Yes |
| spring_security_oauth2_client_registration_oms_redirect_uri | The callback URL in the http://{serverDomain}/login/oauth2/code/{registrationId} format, which is specified by redirectUrl. {serverDomain} is the domain name and {registrationId} does not need to be entered. |
Yes |
| spring_security_oauth2_client_registration_oms_authorization_grant_type | Currently, only the authorization-code mode is supported. | Yes |
| spring_security_oauth2_client_registration_oms_scope | The authorization scope. The value is a list of permission IDs separated with commas (,). openid must be included in the value. |
Yes |
| spring_security_oauth2_client_registration_oms_provider | You can define the value. Example: oidc. | Yes |
| spring_security_oauth2_client_provider_jwk_set_uri | The endpoint used to retrieve the public key of the JSON web key (JWK) for decoding the JWK. | Yes |
| spring_security_oauth2_client_provider_authorization_uri | The authorization endpoint. |
Yes |
| spring_security_oauth2_client_provider_token_uri | The endpoint used to obtain a token. |
Yes |
Example
Replace related parameters with the actual values in the target deployment environment.
oms_meta_host: xxx.xxx.xxx.xxx
oms_meta_port: 2883
oms_meta_user: oms_meta_user
oms_meta_password: ***********
drc_rm_db: oms_rm
drc_cm_db: oms_cm
drc_cm_heartbeat_db: oms_cm_heartbeat
cm_url: http://xxx.xxx.xxx.xxx:8088
cm_location: 100
cm_region: cn-anhui
cm_region_cn: cn-anhui
cm_is_default: true
cm_nodes:
- xxx.xxx.xxx.xxx
tsdb_service: 'INFLUXDB'
tsdb_enabled: true
tsdb_url: 'xxx.xxx.xxx.xxx:8086'
tsdb_username: username
tsdb_password: *************
oms_iam_auth: OAUTH2
oms_oauth2_user_account_name_field: nickname
oms_oauth2_sso_login_url: http://oms.example/org:8090/omsp/oauth2/authorization/oms?oms_back_url=http://oms.example.org:8090
spring_security_oauth2_client_registration_oms_client_id: xxx
spring_security_oauth2_client_registration_oms_client_secret: xxx
spring_security_oauth2_client_registration_oms_redirect_uri: http://oms.example.org:8090/omsp/login/oauth2/code/{registrationId}
spring_security_oauth2_client_registration_oms_authorization_grant_type: authorization_code
spring_security_oauth2_client_registration_oms_scope: openid,profile
spring_security_oauth2_client_registration_oms_clientAuthenticationMethod: client_secret_basic
spring_security_oauth2_client_registration_oms_provider: oms
spring_security_oauth2_client_provider_jwk_set_uri: https:xxx.com
spring_security_oauth2_client_provider_authorization_uri: https://xxxx/api/auth
spring_security_oauth2_client_provider_token_uri: https://xxx/api/token

