Transport Layer Security (TLS) is a cryptographic protocol that provides confidentiality and data integrity between two communicating applications. OceanBase Database extends the original TCP communication to support the SSL/TLS protocol, addressing communication encryption. Encrypted transmission reduces the risk of sensitive information leakage in the database. Encrypted transmission is the process of encrypting and decrypting data using keys, which can effectively protect data security. Specifically, database encrypted transmission can be implemented through the SSL or TLS protocol.
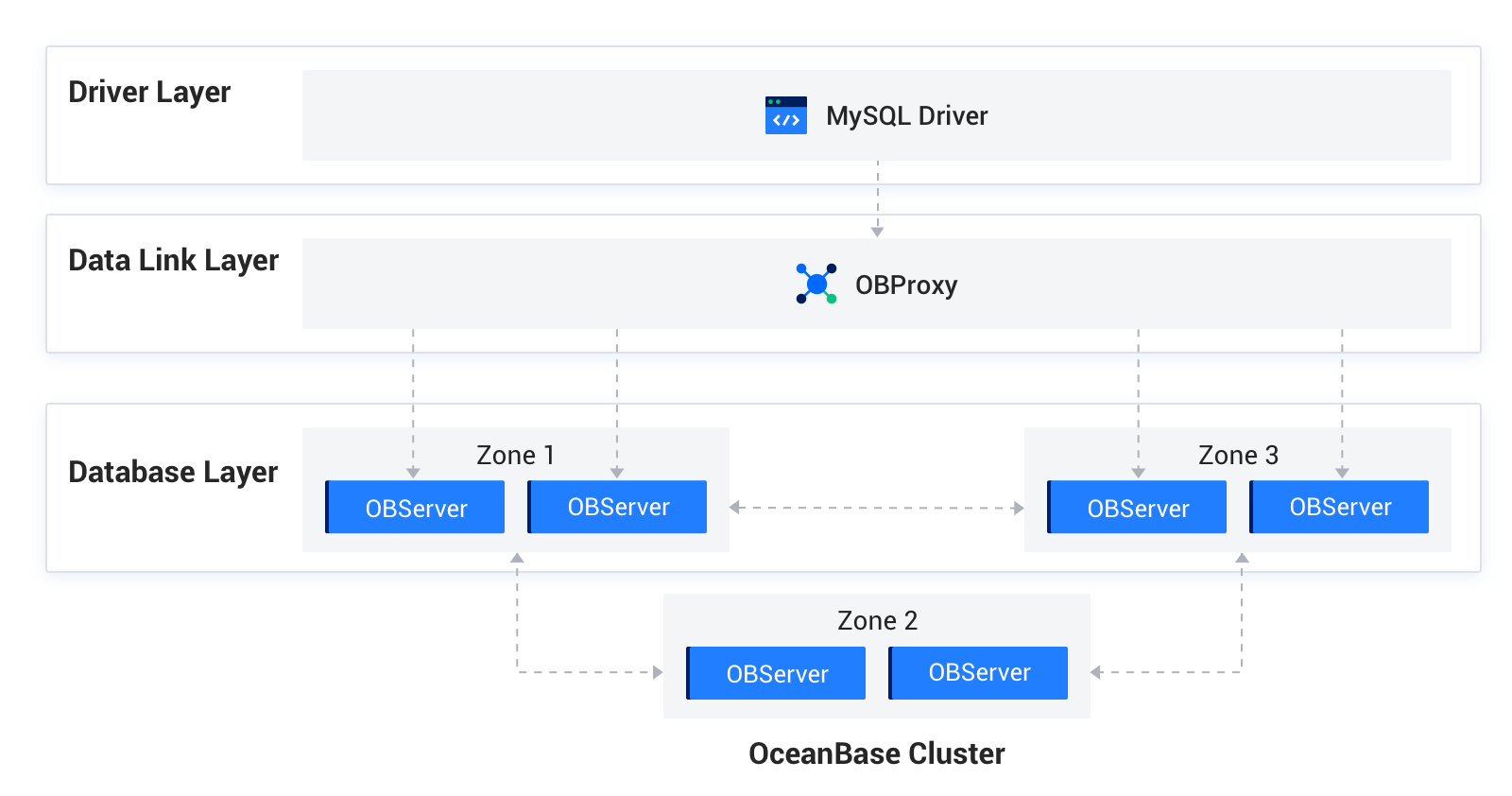
OceanBase Database can be divided into the following three basic parts at the product architecture level.
The following two protocols are used for communication:
MySQL protocol: The driver layer communicates with the data link layer, and the data link layer communicates with the database layer over the extended MySQL protocol. After communication encryption is enabled, it takes effect immediately, and all new MySQL connections use encryption for communication.
OB-RPC protocol: Communication between OBServer nodes, and between OBServer nodes and liboblog, ob_admin, and other components uses the OBServer RPC protocol. Because connections between internal nodes are persistent, after encryption is enabled, internal nodes still communicate in the original non-encrypted mode. Communication encryption between internal nodes takes effect only after you restart the OceanBase cluster.
Components such as OBProxy at the data link layer, OBServer, liboblog, obadmin at the database layer, all support SSL/TLS encrypted communication. They rely on OpenSSL or third-party SSL libraries at the underlying level to provide secure encrypted transmission services for businesses.
OceanBase Database provides different SSL/TLS authentication mechanisms for each user. The options include:
- One-way SSL authentication: The client must load the server's CA certificate. The client unidirectionally verifies the validity of the server certificate.
- X.509 mutual authentication: Both the server and the client must load the peer's CA certificate, and both verify the validity of each other's certificate.
- Special mutual authentication (combinations allowed):
- Authentication with a specified encryption algorithm: Based on X.509 mutual authentication, with a specified SSL encryption algorithm.
- Authentication with a specified issuer: Based on X.509 mutual authentication, with a specified issuer of the client CA certificate.
- Authentication with a specified SSL subject: Based on X.509 mutual authentication, with a specified subject of the client CA certificate.
- TLS passwordless authentication: If the client does not need to verify the identity of the OBServer node, it does not need to load the CA certificate. Otherwise, it must load the CA certificate.

