Transparent Data Encryption (TDE) allows you to encrypt sensitive data on disks, such as the baseline data and clogs. Data is automatically encrypted before it is written to the storage medium and is automatically decrypted when it is read. The encryption process is transparent to users, and authenticated users have unlimited access to the data. When the storage medium is lost, TDE ensures that the sensitive data stored on the medium cannot be accessed by unauthorized users.
Applicability
OceanBase Database Community Edition does not support TDE.
Two-level key system
TDE encrypts and decrypts data in a two-level key system. The minimum encryption granularity is a database table. To encrypt a table, you must put it in an encrypted tablespace. Each encrypted tablespace is configured with an encryption algorithm and a corresponding data key, which are used to encrypt the data in the tablespace. Each tenant has a master key to encrypt the data key for the tablespace. To prevent unauthorized decryption, the master key is stored in the key management service (KMS).
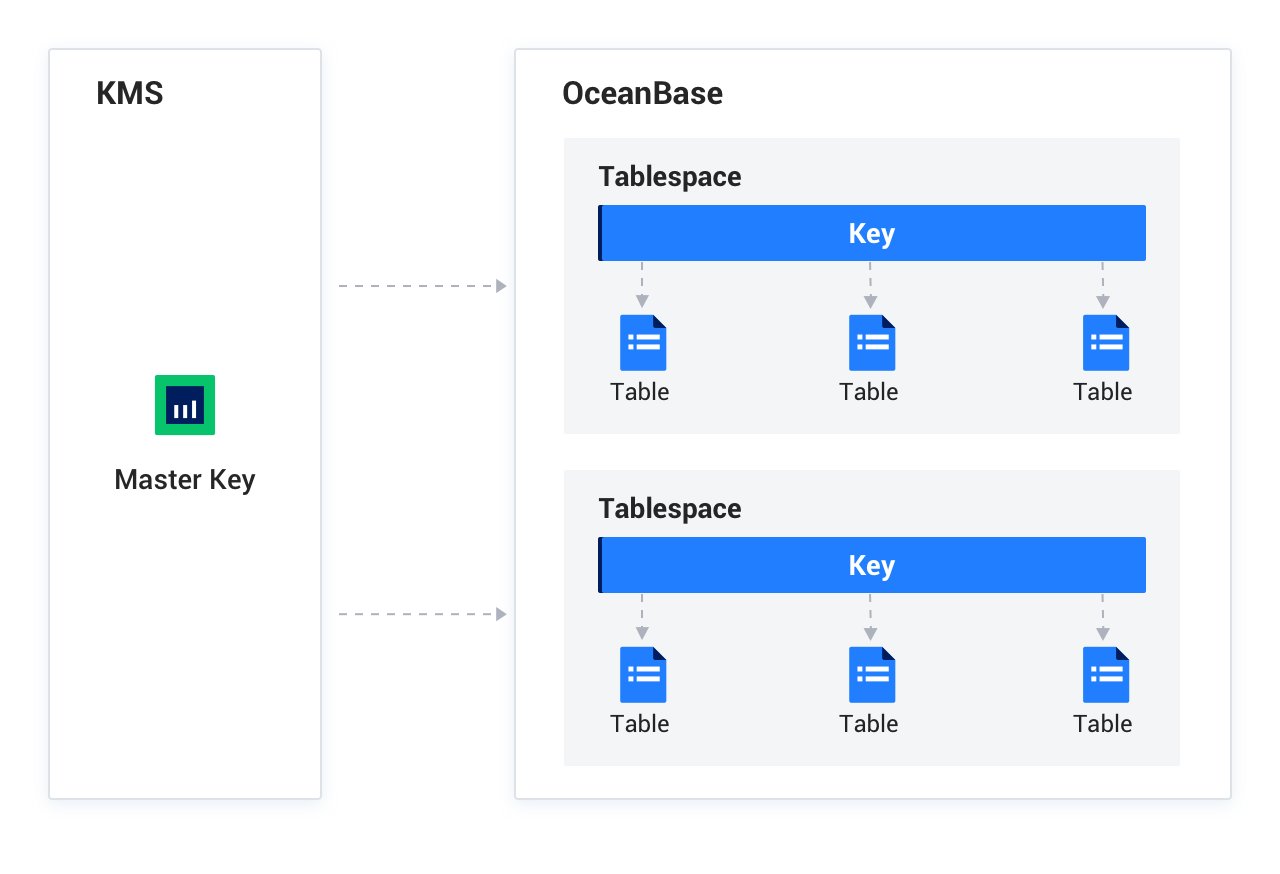
When encryption is enabled, the master key is used to encrypt the data key. The ciphertext of the data key is stored in the internal table, macroblock header, and clog header. The data keys are not stored in plaintext. To encrypt and decrypt the data, use the master key to decrypt the ciphertext and obtain the data key, and then decrypt the user data in the macroblock or clog.
Mechanism of valid encryption
User data stored on the disk includes clogs and macroblock data, and data is encrypted only when it is written to the disk. In-memory data is not encrypted. If you enable encryption for a table that is not encrypted, its existing unencrypted clogs and macroblock data on the disk are not encrypted. Only the subsequent data written to the disk is encrypted. Each clog and each macroblock records encrypted metadata. Therefore, encrypted and unencrypted data can be coexistent.
Clogs are appended to existing ones on the disk. Unencrypted existing clogs remain unencrypted. After you have enabled encryption for a period when the existing unencrypted clogs are recycled, the clog data on the disk are all encrypted. Macroblock data is written to the disk only in minor compactions or major compactions. You can manually trigger a full major compaction to encrypt all macroblocks that are not encrypted.
Supported encryption algorithms
Algorithm |
Key length |
Mode |
|---|---|---|
| AES | 128 bits, 192 bits, and 256 bits | ecb and gcm |
| SM4 | 128 bits | cbc and gcm |

